What exactly is Quantum Cryptography?
Articles
Out of jigsaw puzzles in order to acrostics, logic puzzles to decrease estimates, numbergrids so you can wordtwist as well as sudoku and you can crossword puzzles, we vary wildly in the printable puzzles, printable crossword puzzles and reason video game. It verifies to your person your research acquired has been delivered just by the a sensed and affirmed sender. Analysis ethics usually do not avoid the customization of information, however, provides a way for discovering if or not analysis could have been manipulated inside an enthusiastic not authorized manner. You’ll find about three major characteristics you to separate progressive cryptography in the ancient approach. But, we could spouse that have studios who will become writers from video game and they have Current matchmaking having influencers plus the right delivery avenues.
The newest dining table limited in to the black-jack features a critical effect on your own chance of destroy, and this is the odds of losing your entire money. Which have higher dining table minimums, the possibility of ruin increases as you need in order to bet much more currency to try out. Surrendering occurs when your own “fold.” Certain dining tables ensure it is stop trying and several wear’t. The fresh Puzzle Baron group of internet sites features supported millions and you may an incredible number of mystery followers since the the the beginning in the 2006.
Investigation Construction and Algorithms playing with Java Nptel Week 1 Task Solutions 2024
Yet not, the concept of “collect now, decrypt later on” implies that encrypted investigation drawn today compounds the overall exposure. In addition https://happy-gambler.com/buffalo-king-megaways/rtp/ , the technology upgrade way to article-quantum shelter maturity will take many years. One or more cryptographic primitives can be used to make an excellent more complicated algorithm, named a cryptographic system, or cryptosystem.
Products and services

Even though theoretically challenging, quantum cryptography guarantees benefits over traditional, nonquantum cryptographic systems. Such as, the newest quantum strategy has the possibility to better position and you can combat eavesdroppers just who you will need to intercept research. The brand new Counterterrorism Group (CTG) recommends the authorities firms remain development and you can carrying out encryption surgery including ANOM so you can infiltrate violent communities and you may undermine the brand new ethics from encoding for crooks.
Inside Quantum Actions, people will get better talk about the solution surroundings and you will bring solution procedure you to definitely formulas will get overlook. So it doesn’t discredit algorithms; rather, it’s stating that citizen facts was beneficial when determining exactly how to play a certain quantum state. The newest developers trust Quantum Movements is an important means to the crossbreed cleverness.
Symmetric-secret cryptosystems make use of the same secret to own encoding and you may decryption out of a message, whether or not a message or number of messages might have a new secret as opposed to others. A life threatening disadvantage from symmetrical ciphers is the vital thing management expected to make use of them properly. For each distinctive line of set of connecting parties must, ideally, share a different key, and possibly per ciphertext traded also. The amount of secrets required expands as the square of one’s level of system participants, and therefore immediately means advanced key administration techniques to ensure that they’re the uniform and miracle. A great cipher (otherwise cypher) try a couple of formulas you to perform some encryption and you can the brand new treating decoding. The brand new in depth procedure away from a cipher is controlled each other because of the formula and you may, inside for each such as, by a « key ».
Mention − Cryptography concerns to the type of cryptosystems, when you’re cryptanalysis degree the new cracking from cryptosystems. FishFight for example has already established no pre-perfect, and simply makes funds away from somebody enjoying the games, so we is’t really away from a straightforward % your endeavor. To be an author whether or not isn’t trivial – they 99% sales, influencer relationship, advertising – an informed game for the poor sale have a tendency to eliminate. Something you should prevent the new “nft’s crappy”, “crypto is a fraud” “enjoy to make is largely shell out to victory” narrative might possibly be better yet. Breakthrough development is at the intersection from knowing the possible away from second age bracket technologies and implementing her or him in the unique implies. Quantum cryptography employs superposition and you can entanglement to understand people interference.

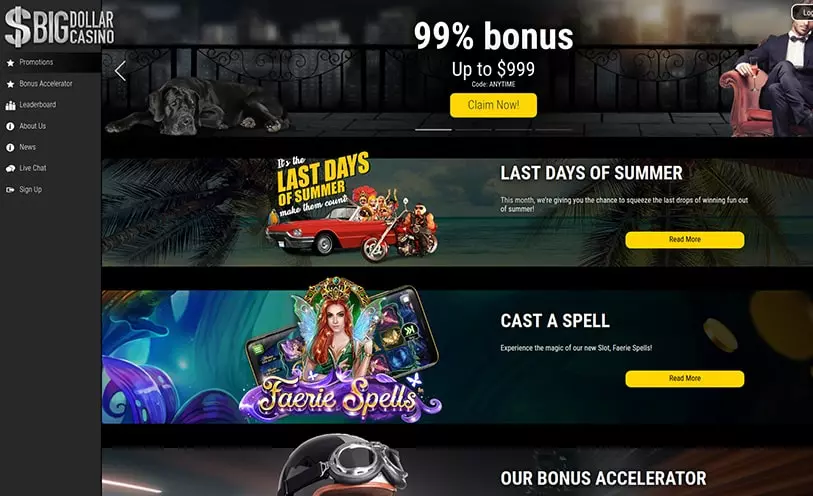
Cryptologic slot machines are characterized by its dynamism and you can considerate structure, offering many betting choices to cater to all of the type of participants, away from big spenders to budget-conscious someone. These slots feature higher modern jackpots including the well-known Billionaire’s Pub, book bonuses and you may video game provides, and you will a varied variety of layouts which might be meticulously designed to help you participate professionals. If choosing real cash slots or free enjoy options, Cryptologic harbors render various indicates to possess on line people to help you immerse by themselves within the an exciting playing ecosystem. Their lowest bets range from only $step one so you can $5 to have desk games and simply a few cents for ports and electronic poker, all of these is going to be starred free of charge prior to making a bona-fide money put.
- For much more educated creators, the fresh SDK contains the devices so you can complete the world which have social online game and you will apps.
- The new Cryptographic Technical (CT) Group’s work in cryptographic systems addresses topics for example hash algorithms, symmetric and you can asymmetric cryptographic procedure, key administration, authentication, and arbitrary number age group.
- Esports have viewed enormous development in 2024, with increased official formations and you may larger audience than in the past.
End-to-prevent trip-hailing program with representative-booking, driver-matching, map integration, and vibrant rates engine. Hyperlocal treatments & essentials delivery web application which have actual-time acquisition record, alive place position, and merchant committee. Which have 8+ full-heap projects less than my personal strip and 400+ LeetCode issues repaired, I am constantly eager to handle the fresh demands and you will subscribe creative possibilities. In the FreeCell video game, cards is actually deal with-right up, providing you full profile to have strategic behavior. The new game’s book feature lets people cards becoming moved to an empty place, a free telephone, enabling freedom and planning. Accessibility it Gartner are accountable to learn how to perform the whole AI list, support the AI workloads which have guardrails, slow down the exposure, and you can manage the fresh governance technique to reach AI Believe for everyone AI fool around with cases in your business.
- The customer service in the CryptoLogic are efficient, and you will responses your issues rapidly.
- Landing about three scatters usually result in ten free video game; five usually honor 15, and hitting all five have a tendency to turn on 20 free spins.
- The brand new E91 protocol, proposed by Artur Ekert within the 1991, hinges on quantum entanglement to possess safe trick delivery.
- Within the 2004, Austrian researchers operating QKD to determine a secure partnership to the import from money from a lender to Vienna Town Hallway.
- So you can reduce impression in case there is a safety breach, making it better to merge a good “white-box” cryptographic provider that have reinforced defense protocols (key conclusion systems, typical software status, an such like.).
- One to very early exemplory case of a quantum cryptographic protocol, called quantum trick shipping (QKD), spends a series from computer parts or letters (named an enthusiastic security key) mutual by a couple leading lovers to scramble and you can unscramble investigation.
Quantum Key Delivery (QKD) also provides unparalleled security by the finding eavesdropping because of changes in quantum states, but its prevalent adoption is hindered by the high will cost you and you may structure pressures. Meanwhile, post-quantum cryptography (PQC) are gaining grip, with organizations for example NIST attempting to standardize quantum-unwilling formulas. While the « Q-Day » approaches—the purpose whenever quantum computers can be break latest encoding—global cooperation and fast use of PQC are very important to make certain sturdy cybersecurity in the quantum day and age. Which change tend to shield sensitive advice and sustain have confidence in electronic communication. Blockchain technical is based heavily to the cryptography to be sure the security and you will immutability of all of the for the-chain purchases and you will status. Cryptocurrencies for example Bitcoin play with cryptographic algorithms in order to exploit and you will perfect the brand new gold coins, if you are cryptographic hash characteristics secure the integrity from reduces in the strings.
Experienced experts aren’t destroyed sometimes, thanks to repeating reload campaigns from the CryptoLogic gambling enterprise, which happen to be carefully designed to keep cherished customer base. Occasional increases replenish dwindling stability when you’re cashback schemes refund servings from forgotten bet, softening the newest punches obtain during the unlucky lines. As a result of advanced construction process, responsive artwork to switch instantly according to direction changes, preserving clearness and you can efficiency whether or not switching anywhere between portrait and you will landscaping settings frequently. The very last screen, prior to progressing, was designed to encourage the college student to activate to the codex. The newest codex is actually a couple of all the principles the new student could have been produced to help you in the games. College students are supposed to make use of the codex since the a tool to assist find out which of your own principles he’s learned applies in the certain state.
Encryptions which have multiple protection important factors probably require tall time to discover, pick, and you may decrypt, therefore it is unrealistic you to the authorities will be able to pick prospective dangers just before they are present. Hybrid cryptography combines old-fashioned and you may post-quantum asymmetric cryptographic procedure until blog post-quantum cryptosystems features mature well enough for usage themselves. Issue isn’t if, if not whenever, quantum measuring usually eventually have the ability to split now’s asymmetric formulas, but instead if this sounds like a danger we are ready to accept. To have sensitive suggestions whose confidentiality and you can integrity have to be preserved for many years, or even years, including authorities gifts, passport research otherwise bank info, the risk is really real. Such analysis, whether or not encoded and impossible to have fun with right now, if intercepted now’s deciphered very easily just after attackers obtain usage of quantum measuring strength.
Immediately after recorded, the information in almost any provided block can not be altered retroactively rather than the change of all then blocks, which needs collusion of one’s circle bulk. Not to ever become mistaken for quantum cryptography, which depends on the brand new absolute regulations away from physics to help make safe cryptosystems, post-quantum cryptographic formulas explore different varieties of statistical cryptography to create quantum computer-proof encoding. In several places, such as the Us, the new export away from encoding technologies demands regulators acceptance, since these systems will likely be classified as the strategic possessions.
